There are no boundaries that scammers won’t cross to fraudulently cash out on ad revenue at the expense of advertisers. Just like there are good bots and bad bots, good proxy traffic and bad proxy traffic, fraudsters sabotage your ad campaigns with malicious iFrame traffic — a usually legitimate method of embedding one webpage into another.
To help you understand why preventing bad iFrame traffic is so important, we explore how it works, the threats it poses to your ad campaigns, and the solutions you must implement to prevent it from damaging your revenues.
What is iFrame traffic?
iFrames are web elements that facilitate the insertion of external content from another URL or other web pages into a webpage. For example, social media widgets and YouTube videos are commonly inserted into web pages. So, iFrame traffic is simply traffic that derives from the iFrame content. That doesn’t make it necessarily “bad” traffic. In fact, in many cases, there is no harm done or intended.
However, iFrame traffic is also an ad fraud technique that scammers employ to exploit user interaction with web pages and to profit from unsuspecting advertisers. In this case, it is a major problem for advertisers.
How does iFrame traffic fraud work?
Traffic that comes from iFrames can be derived from legitimate use cases and is not fraudulent 100% of the time. However, fraudsters can use iFrames to load entire pages in a window of 0px height and 0px width — meaning the content is invisible to the user. This poses a vulnerability when it’s used to generate false visits or to deceive the user into clicking something they don’t intend to.
iFrames can also load “transparently” on web pages, and fraudsters use this vulnerability to intercept user clicks on this top layer to invisibly coerce them into clicking on other areas of the page, such as a purchase button.
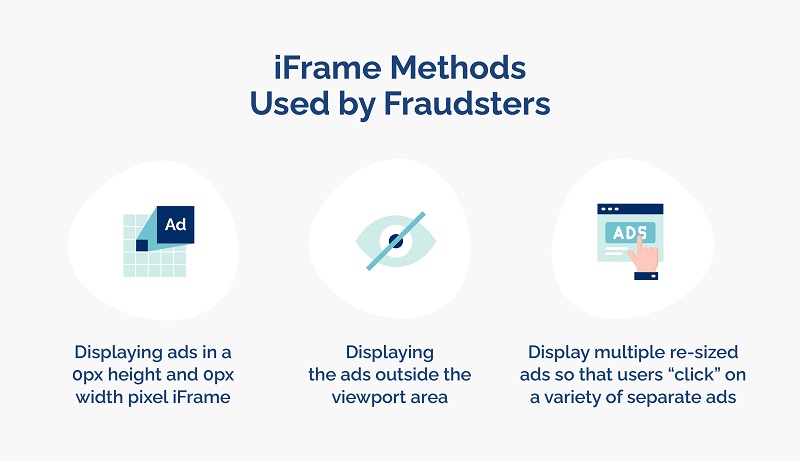
Fraudsters use iFrames to hide ads on web pages and receive credit for fraudulent impressions. They can do this by using one of the following methods:
- Displaying ads in a 0px height and 0px width pixel iFrame
- Displaying the ads outside the viewport area (also known as the visible parts of the webpage)
- Display multiple re-sized ads so that users “click” on a variety of separate ads
How does iFrame traffic fraud affect your ad campaigns?
In terms of its threats, iFrame traffic can be used to carry out:
- Impression fraud
- Click fraud
- Lead fraud
- Subscription fraud
- Attribution fraud
However, regardless of which of these methods is applied, the end result for advertisers is the same: Drained budgets that yield no results, misleading campaign data, and lost opportunities to invest in legitimate ad traffic sources.
What can you do to prevent fraudulent iFrame traffic and its negative impact on your campaigns?
iFrame traffic affects organizations when iFrames are being used as a vehicle to make users click something they don’t intend to (also known as clickjacking) or to load a page that is hidden from the user page by using a very small iFrame. Organizations can apply some configurations to their landing pages to avoid being “iFramed”.
However, to check if you are receiving iFrame traffic, you’ll need to run an iFrame detection mechanism. This is usually done by running certain code within your website — something Opticks can implement swiftly.
Opticks can also detect and block iFrame traffic from the get-go and can distinguish between very small iFrames (an indicator for fraud) and normal-sized iFrames, which is useful for allowing good iFrame traffic to get through where it should.
Defend your organization against malicious iFrame traffic
If you suspect that you’ve become a victim of fraudsters using bad iFrame traffic, it’s time to take action. Anti-fraud solution Opticks can detect and prevent bad iFrame traffic before it has a chance to drain your ad spend.
To learn more about how the expert team at Opticks can help protect your organization, contact our team here for a free demo or start your free trial.